// PROTOCOL: SHIELD_REACTIVE
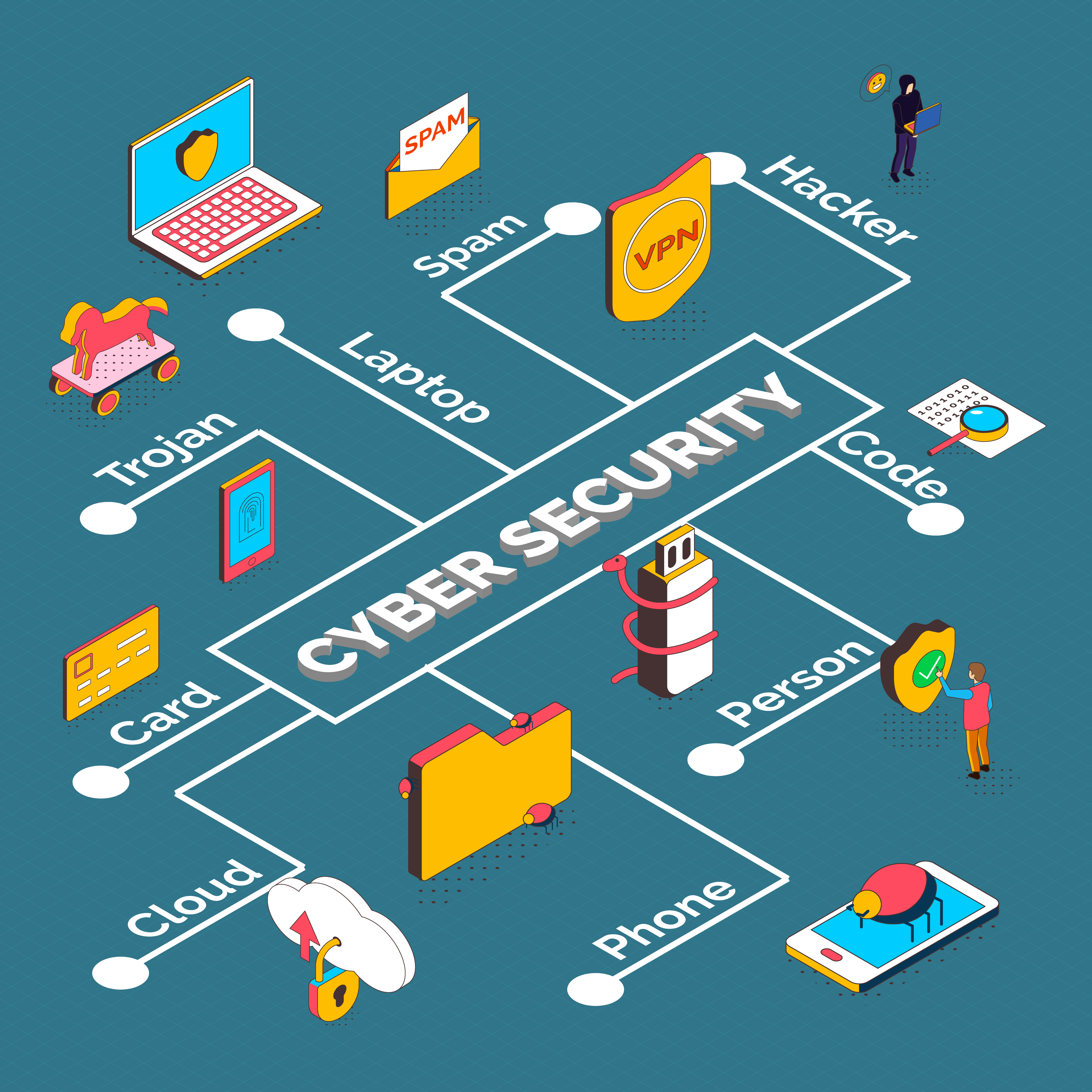
CYBER SECURITY
Active counter-measures and zero-trust architecture deployed at the edge of the global quantum network.
Threat Mitigation
Autonomous detection agents identify and isolate malicious patterns before they penetrate the first layer of the neural net.
- > PACKET_INSPECTION: ACTIVE
- > IPS_BYPASS_SHIELD: STABLE
- > BRUTE_FORCE_LOCKOUT: ENABLED
Quantum Encryption
Utilizing lattice-based cryptography to ensure data remains sovereign, even against the compute power of a 2048-qubit processor.
- > KEY_ROTATION: 120ms
- > ALGORITHM: CRYSTALS-Kyber
- > ENTROPY_LEVEL: CRITICAL_MAX